It’s hard for contemporary demosceners to imagine, but back in the 1980s, when much of the scene‘s activity evolved around pirated games, and the separation between “illegal” and “legal” scenes was far from complete,1 sceners were always conscious of the potential for unwanted contact with the police – at least in countries like Germany, where software pirates became a target for law enforcement as early as in the mid-1980s. Even those who defined themselves as “legal guys” were not completely safe from an unpleasant encounter with the police: Copyparties, potential targets for police raids, were attended by demo coders just as much as by crackers and swappers; a contact address of a musician or an intro programmer in a scrolltext could be easily mistaken by law enforcement for that of a “dangerous” pirate; and, after all, who didn’t own at least a few cracked games? Nearly everyone knew someone who was “busted” but, of course, every scener was convinced that they would not be the next. As an Amiga BBS veteran put it recently: “It was like being on the surface of the Moon: Sometimes a meteorid strikes here and there, but one still feels safe.”2 Some sceners managed to stay “unbusted” during their whole career, even while being knee-deep in the “illegal business” – but many didn’t.
Since proceedings in the 1980s against alleged and real software pirates took place in a very recent past, it’s not really possible to explore the events from the perspective of law enforcement through archival work. However, some veterans kept the documents that were handed to them in the course of investigations. We are highly indebted to Marty of the (in)famous C64 cracking group Radwar Enterprises 1941 for providing us with documents from the investigation against him in late 1989.
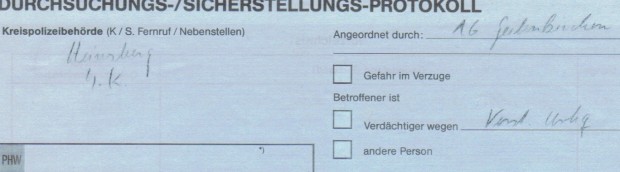
The first page is the house search warrant from 6 November 1989, issued on “suspicion of illegal circulation of copyright-protected software”. The following two pages (the ones on blue paper) constitute the protocol of the house search, which took place some two months later; the second page confirms the confiscation of 1,157 (!) C64 floppy disks. However, as it was often the case, the criminal proceedings were ceased a mere month later, in January 1990, due to the classification of the accused as a “young offender”; the corresponding resolution (page 4) expresses hope that “in the future, [the accused] will abide by the law”.
Here is Marty’s story of the whole affair:3
“In 1988, I was drafted into the army and thus sold everything from my C64 collection in order to buy a reliable car to drive to the barracks in. However, while I sold everything else – computer, disk drives, printer, books, magazines – I kept a part of my (rather large) collection of disks, about 2,000 of them. […] After getting rid of all my hardware, I also slightly distanced myself from the scene and only seldom got in touch with my Radwar mates. At that time, I had discovered the opposite sex, and that’s what preoccupied me more. […] Shortly before the house search took place, the father of my then-girlfriend brought me his C64 and a 1541II [disk drive] in order for me to upgrade his system with SpeedDOS.4 The disks which I kept were safely stored in my granny’s attic. However, in order to do some testing, I brought them back to my parents’ place. Shortly before that, I incidentally bumped into MWS [/Radwar] and he gave me his latest releases. It must have been around 100 of his disks that were confiscated together with mine in the end. Having a computer at my fingers again, the scene virus began to set in…
After I had refurbished the computer, I had to give it back, but I still kept a 1541 (which I bought for test purposes) and the disk collection at home. Then the house search took place. Superintendent Dolenz took all disks with him and left me with the 1541, since I couldn’t do anything illegal with it. During the house search I got to know that there had been a bust in the Ruhr area during which my address was found in an address book. I assume that it was the house search at Jeff Smart’s place, since they indeed found his address book,5 so I got caught up in that.
The criminal proceedings took their course, and I had to come to the police station and give a statement. The police must have noticed that MWS’s disks were encrypted with COP-SHOCKER, because they asked me for the “decryption sequence”, but I didn’t tell them anything because I didn’t want to incriminate myself.6 However, they seemed to have forgotten about the encryption in the course of the proceedings, since I was never again asked about it. […] Anyway, the case went through the system for a few weeks, and, probably since they found only disks and no further evidence of any commercial business with cracked software, the criminal proceedings were ceased in the end. I even got some of the disks back, namely those protected with COP-SHOCKER and those which were empty or unreadable. I think I got around 300 disks back.”
You can download high quality scans of Marty’s documents here.
PS: Thanks to Syphus for late-night proofreading!
- See most recently on this complex process: Reunanen, Markku. „How Those Crackers Became Us Demosceners.“ WiderScreen, no. 1–2 (2014). http://widerscreen.fi/numerot/2014-1-2/crackers-became-us-demosceners/
- Interview with Hamster/TRSI, Saarbrücken/Germany, 4 April 2015.
- Mail from Marty/Radwar, 29 November 2015. Translation from the German, G.A.
- SpeedDOS was a “fastloader” hardware add-on for the C64, allowing quicker loading times for software. Intriguingly, it was developed in 1984 by two first-generation crackers, who sold the hardware commercially. See https://www.c64-wiki.de/index.php/SpeedDOS
- Jeff Smart was the editor of the C64 crackers’ magazine “Illegal” (see our previous post). His house search took place on 17 May 1989, during which the police found his address book hidden in a record sleeve (See http://csdb.dk/release/?id=123909).
- Cop-Shocker was an encryption tool for the C64, developed in 1989 by MWS/Radwar and commercially marketed through Digital Marketing, a software company/PD service MWS was involved with. The tool hid the disks’ filelist, making the disks appear empty. The program was immensely popular, and, ironicaly, there were other crackers who “cracked” it just like any other commercial piece of software. See http://csdb.dk/release/?id=67400